Haja Mo
I need to tell you something that has been eating at me for a very long time.
I have been in the cybersecurity industry for over 25 years. I have personally conducted thousands of training sessions across dozens of countries. I have stood in front of classrooms in New York, Dubai, Kuala Lumpur, Chennai, London, Singapore — everywhere. I have watched tens of thousands of students go through cybersecurity training programs.
And for years I carried a pain that I couldn’t solve.
Let me explain what I mean. And I promise you — if you work in cybersecurity, if you’ve ever taken a certification course, if you’ve ever tried to implement what you learned in training into a real production environment — this will hit you right in the chest.
THE PROBLEM THAT NOBODY IN THE INDUSTRY TALKS ABOUT
RCCE training has hundreds of labs — all running inside Rocheston Rose X, our massive 1.2 terabyte cybersecurity operating system that I built from the ground up. Rose X is not a repackaged Linux distro. It is a purpose-built OS containing every hacking tool, every framework, every vulnerable application, and every lab environment our students need. Over 4,200 hands-on labs. Updated every single week. And they are FANTASTIC. I am genuinely proud of every single one of them. Students love them. The feedback is incredible.
We teach dark web operations. Ransomware containment. XDR deployment. Threat hunting. Malware analysis and removal. Incident response workflows. Web application firewalls. DLP and encryption. Vulnerability assessment. Compliance frameworks. Exploit writing. Penetration testing. Asset discovery. Zero-Trust, Red team versus blue team exercises. SOAR automation. AI-powered cyberattack simulation. DevSecOps pipelines. Cloud security management. Threat intelligence. Digital forensics. SIEM operations.
I can keep going for another hour. The RCCE curriculum is massive. Over 1,039 courses. Over 5,954 hours of content in CyberNotes. Every major cybersecurity domain covered in depth.
The labs work brilliantly. Students walk away with real hands-on skills.
But here is the problem that kept me awake at night.
NONE OF THESE LABS TALK TO EACH OTHER.
The dark web lab uses one set of tools. The ransomware containment lab uses different tools. The XDR lab runs on one vendor’s platform. The vulnerability scanner is a completely separate product. The SIEM is another product. The firewall is another. The endpoint tool is another. Every single lab is an island. Beautiful islands. Impressive islands. But islands.
Different tools. Different vendors. Different GUIs. Different configuration files. Different reporting formats. Different rule syntax. Different dashboards. NOTHING is connected. NOTHING shares data. NOTHING presents a unified picture.
The student learns 30 different tools across 30 different labs with 30 different interfaces and 30 different vendor philosophies. And that mirrors exactly what is broken in the real world. But I am supposed to be PREPARING students for the real world — not recreating its problems in the classroom.
Here is the moment that broke me. I watched a brilliant RCCE student, Sheela finish the entire Level 1 program. Top marks on everything. Could run network scans in her sleep. Could craft exploit payloads. Could analyze IOC packet captures. Could write YAML detection rules. Could perform incident response. She was genuinely talented.
Then Sheela went to her first job. On day three she called me. She said: “Haja Sir!, I know how to use all these tools individually. But how do I make them work TOGETHER? How do I get my vulnerability scanner to feed into my SIEM which triggers my SOAR which notifies my XDR which isolates the host? None of these tools talk to each other. Everything I learned was in isolation. The real world is integration. And I don’t know how to integrate.”
That phone call haunted me.
She was right. I had taught her 30 tools. But I had not taught her how to fight a unified battle. Because no unified platform existed to teach it on.
THE FIRST ATTEMPT — VULNERABILITY VINES
I did not sit with that pain. I built.
The first answer was Rocheston Vulnerability Vines. I took the best open-source cybersecurity tools available in the industry — vulnerability scanners, asset discovery, endpoint detection, SIEM integration, compliance frameworks, WAF, penetration testing, DevSecOps pipelines, threat intelligence feeds — and I packaged them into one beautiful unified platform.
Vines was a breakthrough. For the first time RCCE students had a real platform they could take to their jobs. Not a training lab that disappears after class. A real deployable tool. They could walk into an organization on day one and implement asset discovery, run vulnerability scans, configure compliance baselines against NIST 800-53, deploy endpoint agents, set up phishing simulations, launch awareness training, configure dashboards, and generate executive reports. All from one platform. All with tools they trained on.
I gave Vines exclusively to RCCE students. No charge. No license fee. Just — here, go secure your organization.
And it worked. RCCE engineers started deploying Vines in real enterprises. Doing real vulnerability assessments. Running real compliance audits. Generating real reports. On day one. Without waiting for procurement to approve a six-figure tool purchase.
But even Vines didn’t fully solve my original pain.
You can learn more about Vines here rocheston.com/vines
THE DEEPER PROBLEM — THE ENTERPRISE TOOLS I COULDN’T SHOW
Here is something that every cybersecurity trainer deals with but nobody admits publicly.
The enterprise platforms used in the industry — the ones made by the major vendors — they are powerful. The XDR platforms. The SIEM platforms. The cloud security platforms. The SOAR platforms. I have tremendous respect for what those engineering teams have built. As a trainer I would LOVE to demo these to my students. I want to show them what an enterprise SOC dashboard looks like. I want them to see how threat correlation works at scale. I want them to understand how automated containment orchestrates across network, endpoint, cloud, and identity simultaneously.
But I CAN’T.
There is no demo to download. There is no trial version for educators. There is no training sandbox provided by these vendors for classroom use. They sell to enterprises for hundreds of thousands of dollars. They don’t give free access to certification trainers.
So what do I do in class? I show screenshots. Static images from marketing pages. Maybe a recorded demo video from a conference keynote. And I say “this is approximately what it looks like” while knowing that my students are getting a watered-down secondhand experience of tools they should be operating with their own hands.
And honestly — even those screenshots? I have no idea how the internal workflows actually function. I can’t show the configuration. I can’t show the rule engine. I can’t show how alerting connects to containment. I’m showing the outside of a building and pretending I know what every room looks like inside.
That is not training. That is a slideshow.
And it gets worse. Even if I could demo these enterprise platforms, I still face the original problem — none of them talk to each other. The enterprise world is just as fragmented as the training world. The XDR doesn’t natively integrate with the vulnerability scanner. The SIEM doesn’t natively feed the SOAR. The cloud security platform doesn’t natively coordinate with the firewall. Companies spend millions buying these tools and then spend millions more trying to make them work together with custom API integrations, middleware, and duct tape.
So even the REAL WORLD doesn’t have what I wanted to show my students — a unified, integrated, beautiful cybersecurity platform where everything talks to everything.
It doesn’t exist.
Or it didn’t.
THE PROGRAMMING LANGUAGE PROBLEM — ZELC
And there was ANOTHER pain that had been building for years.
I watched my students learn Python for scripting. Bash for automation. PowerShell for Windows administration. SQL for database queries. JavaScript for web security. Go for tool development. Six different languages across six different domains.
And NONE of these languages were designed for cybersecurity.
Python is a general-purpose language. It works. But when a SOC analyst writes a Python script to isolate a compromised host, they’re stitching together generic libraries, writing boilerplate network code, handling errors that have nothing to do with security, and producing output that doesn’t integrate with anything else. The language doesn’t understand what an IP address IS. It doesn’t understand what an incident IS. It doesn’t know what containment MEANS. You’re translating security concepts into generic programming constructs and losing meaning at every step.
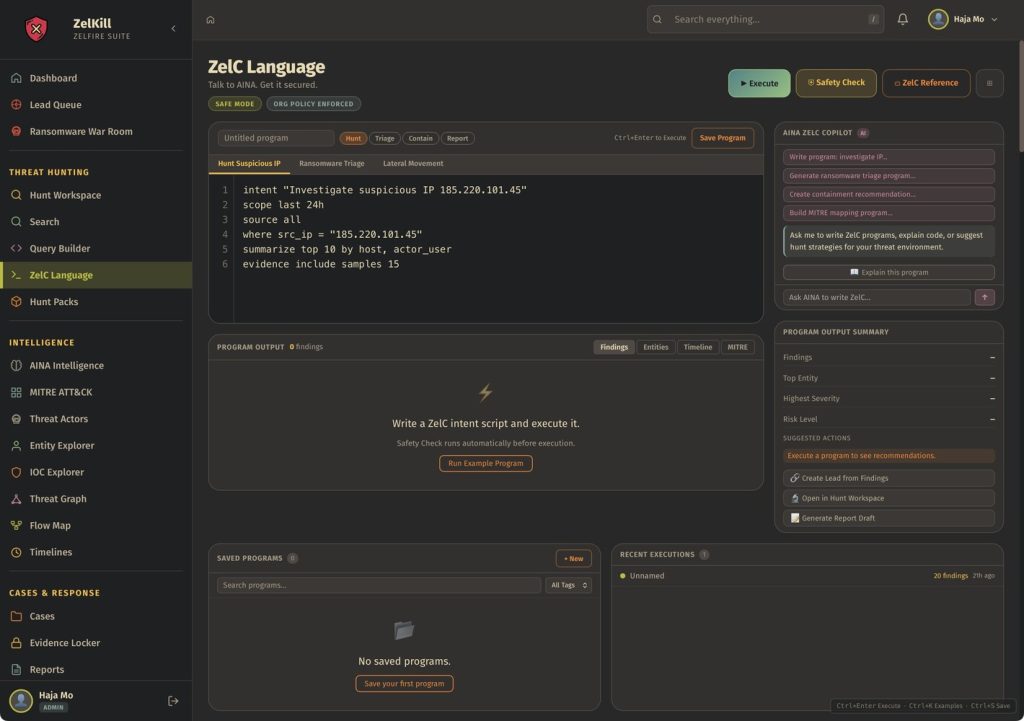
I kept thinking — why isn’t there a programming language that SPEAKS cybersecurity natively? Where IP addresses, CIDR ranges, file hashes, user identities, incidents, timelines, evidence packs, and risk scores are TYPES in the language itself? Where you can write “isolate host” and the language KNOWS what that means across your entire security stack? Where every action automatically produces forensic evidence? Where security permissions are enforced at the compiler level, not as an afterthought?
That language didn’t exist. So I built it.
ZelC is the world’s first cybersecurity programming language. It’s not Python with security libraries bolted on. It’s a language designed from the ground up where security IS the grammar.
Capability-first permissions — code cannot touch network, files, IAM, cloud, or EDR unless the capability is explicitly granted. No hidden powers. No implicit access.
Taint types — untrusted data is tracked at the type level. Tainted values cannot reach sensitive actions until they are explicitly sanitized. Injection attacks become compile-time errors. Not runtime surprises.
Evidence objects — every remediation and every decision produces immutable evidence records with cryptographic hashes and full provenance chains. Built for auditors. Built for compliance. Automatically.
SOC-native primitives — IP, CIDR, Hash, UserId, Incident, Timeline, IOCSet, EvidencePack, RiskScore, ControlId are all first-class types. No more treating an IP address as a string. No more treating an incident as a dictionary. Security concepts ARE the type system.
And ZelC speaks directly to every Zelfire module. One command to ask AINA a question. One command to ingest events into Zelfire. One command to isolate a host. One command to block an IP. One command to generate a compliance evidence pack. The gap between security INTENT and security EXECUTION is one line of code.
Now when I teach my students automation, they don’t cobble together Python scripts with generic libraries. They write ZelC programs that are readable, auditable, evidence-producing, and natively integrated with the entire Zelfire stack. The language itself enforces security best practices. You literally CANNOT write insecure code in ZelC because the compiler won’t let you.
You can learn more about ZelC at rocheston.com/zelc
THE OBSESSION — BUILDING ZELFIRE
I remember the exact moment. I was reviewing RCCE lab feedback and a student wrote: “The labs are amazing individually but I wish I could see how everything connects in a real SOC environment.”
I closed my laptop. I sat in the dark. And I said out loud to nobody: “Fine. I will build the entire thing myself.”
That was the beginning of Zelfire.
I didn’t start with a business plan. I didn’t do market research. I didn’t hire a product team. I started with a question: what would the PERFECT cybersecurity platform look like if one person designed every single module to work together from day one?
No integrations. No API duct tape. No vendor compromises. One architecture. One data model. One visual language. One brain.
And I built it. Module by module. Dashboard by dashboard. Feature by feature. Pixel by pixel.
ZelWall — because every defense starts at the perimeter. A firewall and WAF that doesn’t just block traffic but feeds intelligence directly into the correlation engine.
ZelXDR — because detection without context is noise. An extended detection and response platform with visual attack timelines, AINA AI correlation at 84-90% confidence, escalation intelligence, and temporal cluster analysis that predicts WHEN attacks will hit before they happen.
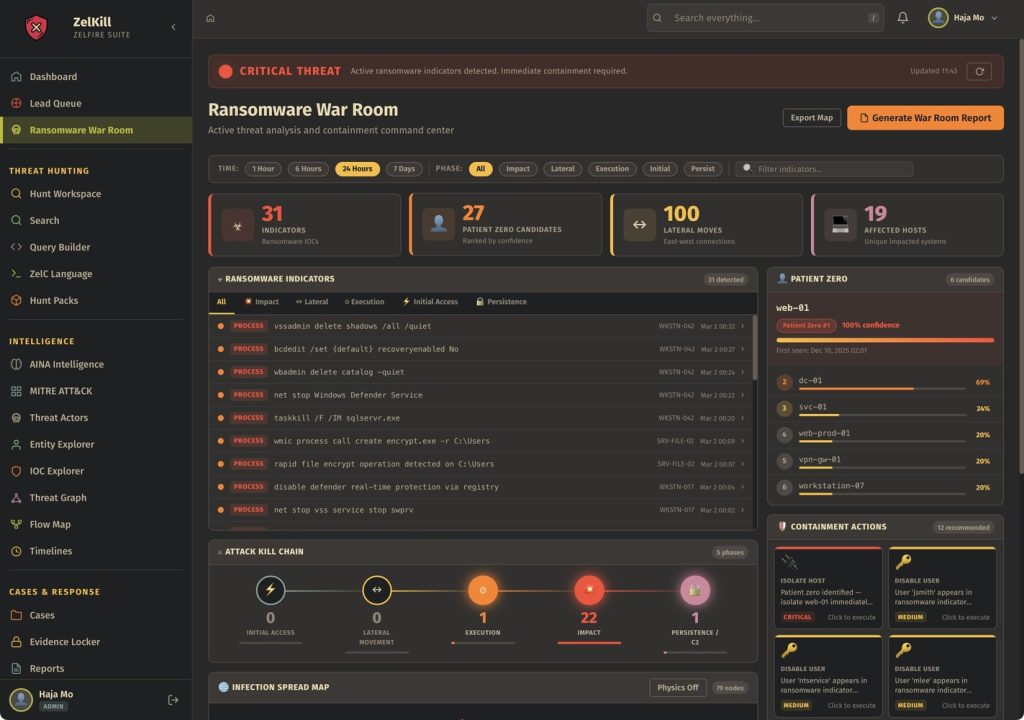
ZelKill — because containment must be autonomous. A multi-layer killswitch that simultaneously commands the firewall to sever connections, quarantines compromised hosts, locks down cloud storage, and logs every action with forensic evidence chains. Containment in under 3 minutes. Not 3 hours.
ZelMap — because you cannot protect what you cannot see. Real-time attack surface mapping with risk scoring. Every asset. Every exposure. Every blind spot. Visible instantly.
ZelScan — because finding vulnerabilities without context is just creating a longer to-do list. AI-powered scanning with risk ranking so you know which 3 out of 10,000 CVEs actually matter.
ZelCloud — because multi-cloud security is a lie until someone unifies it. AWS, Azure, GCP — one dashboard, one risk score, one set of controls. CSPM, CIEM, DSPM, Kubernetes, containers, serverless — all in one graph.
ZelSOAR — because automation without intelligence is just faster mistakes. Orchestration that shares a brain with every other Zelfire module.
ZelAccess — because identity IS the new perimeter. IAM, SSO, zero-trust access — integrated natively with threat detection.
ZelZero-Trust — because every vendor claims zero trust and almost none deliver it. Continuous verification and enforcement that actually works because it’s connected to everything.
ZelCode — because shift-left means nothing if your security tools don’t understand code. SAST, DAST, DevSecOps built into the development pipeline.
ZelTester — because penetration testing should be continuous, not annual. Integrated pentesting that shares findings with the vulnerability scanner and the SIEM simultaneously.
ZelRank — because threat intelligence without prioritization is just a news feed. An engine that tells you what matters FIRST.
ZelDrift — because the configuration that was perfect on Tuesday is a disaster by Friday. Continuous drift detection.
ZelPosture — because if you can’t see your security posture in real time, you don’t have one. The SOC dashboard that tells you what is wrong before you ask.
ZelExploits — because thinking like an attacker requires attacker-grade tools. Offensive security intelligence integrated with defensive operations.
ZelC — because the gap between security intent and security execution should be one line of code. The cybersecurity programming language that speaks directly to every module.
And at the center of ALL of it — AINA. Not a chatbot. Not a search bar. An AI intelligence engine that reasons across every module. She correlates. She prioritizes. She sequences remediation with time estimates. She maps kill chains. She predicts attack patterns. She writes executive briefs. She shows her reasoning. 92% confidence. Full explainability. No black box.
16 modules. One architecture. One brain. One programming language. One visual identity — the Obsidian dark theme with Solar Orange accents. Every dashboard designed to be simultaneously functional AND beautiful. Because enterprise security tools don’t have to be ugly. That is a choice the industry made out of laziness. I made a different choice.
THE MOMENT EVERYTHING CHANGED
The first time I stood in front of an RCCE class with Zelfire loaded on the screen, the room went quiet.
I showed them ZelXDR. 20 active incidents. 7 critical. AINA correlating a credential abuse campaign across endpoints and identities in real time. Attack timeline rendering the entire kill chain visually. Remediation sequence prioritized with time estimates.
A student raised his hand and said: “Wait. This is what we’ve been learning in fragments. But now I can see how EVERYTHING connects.”
THAT was the moment I had been chasing for 25 years. That was the phone call from that student answered. That was the pain resolved.
Now when I teach ransomware containment, I don’t use a standalone lab. I show it inside ZelXDR with AINA detecting the payload, ZelMap showing the blast radius, ZelKill containing the threat across network, endpoint, and cloud simultaneously, and ZelWall updating the firewall rules in real time. One screen. One flow. One complete picture.
When I teach threat hunting, students don’t use separate tools for log analysis, network monitoring, and endpoint investigation. They use ZelXDR with AINA highlighting anomalies, write hunt queries in ZelC that produce auditable evidence automatically, and ZelRank provides threat intelligence context. Everything connected. Everything producing evidence. Everything speaking the same language.
When I teach cloud security, students don’t look at screenshots of platforms they can’t access. They USE ZelCloud. Real dashboards. Real configurations. Real multi-cloud environments. Hands on the controls.
When I teach compliance, students don’t read frameworks from PDFs. They implement controls in ZelPosture, validate them in ZelDrift, generate evidence packs, and produce audit-ready reports from ZelScan. End to end.
When I teach automation, students don’t write fragile Python scripts with generic libraries. They write ZelC programs where security operations are native language constructs, every action produces evidence, and the code integrates directly with the entire Zelfire stack. One line of ZelC does what 50 lines of Python approximates.
When I teach SOC operations, students don’t stare at slides showing what a SOC dashboard “might look like.” They sit in front of ZelXDR with AINA running at 90% confidence, processing incidents across every domain, explaining her reasoning, and recommending actions with time estimates. They make real decisions on real data in a real unified console.
THAT is what cybersecurity training should look like. Not 30 islands. One continent.
AND NO — YOU CANNOT BUY IT
Here is the part where I will save you the time of emailing me to ask about enterprise pricing.
Zelfire is not for sale.
There is no enterprise license. There is no reseller channel. There is no “contact sales” button. There is no annual subscription. There is no free trial.
Zelfire is exclusively available to Rocheston Certified Cybersecurity Engineers. If you want the power of Zelfire in your organization, you do not call a sales rep. You hire an RCCE. Or you become one.
I did not build Zelfire to compete with vendors for market share. I built it to solve a training problem that haunted me for 25 years. The solution turned out to be the most advanced unified cybersecurity platform in the world. And I am keeping it exactly where it belongs — in the hands of the engineers I train.
Every RCCE student now trains on enterprise-grade tools from day one. Not toy labs. Not demo screenshots. Not borrowed open-source utilities. Not static slides of platforms they can’t touch. Enterprise-grade unified cybersecurity tools built from scratch to work together as one organism.
When they finish RCCE, they don’t leave with just a certificate and a badge. They leave with the ability to operate a 16-module cybersecurity weapon system. They leave knowing ZelC — a programming language built for security operations. They leave with Vulnerability Vines for real-world deployment. And they take ALL of that ability into every organization that hires them.
I now stand in front of every RCCE class with the most advanced cybersecurity platform in the world loaded on my screen. Every concept I teach has a live module to demonstrate it. Every workflow has a unified dashboard to operate it. Every student can touch, configure, break, fix, and master every tool — because I built every tool myself and I designed them all to work together.
The 25-year pain is finally gone.
This is what happens when you refuse to accept that broken is normal. 16 products. One vision. One architecture. One brain. One language. Built to solve the one problem that nobody else in the industry was willing to admit existed.
The tools don’t talk to each other. Now they do.
Built with 💛 by Haja Mo
rocheston.com/zelfire